Cosmic Node Start 317-794-0655 Unlocking Caller Data Research
Cosmic Node’s initiative examines how caller metadata can be analyzed without exposing personal identifiers. The approach prioritizes governance, consent, and transparent workflows. It emphasizes provenance, stratified anonymization, and auditable access controls to guide ethical decision-making. The goal is to connect signals to actions while preserving autonomy. A careful balance remains to be struck, inviting stakeholders to consider how such practices might unfold in practice and what questions still require answers.
What Cosmic Node Unlocks in Caller Data Research
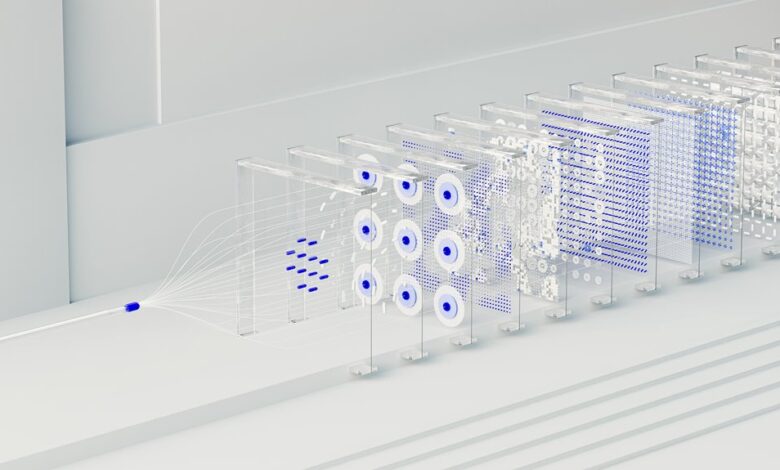
Cosmic Node unlocks insights into caller data by enabling structured access to aggregated information while preserving privacy. It presents Caller identifiers and metadata schemas in secure, standardized formats, supporting transparent Analysis workflows. The system aligns with consent frameworks, minimizing exposure while maximizing usable signals. Researchers assess ethics, privacy, and freedom, ensuring responsible use and trustworthy conclusions without compromising individual rights.
Mapping Call Metadata: From Signals to Insights
In the context of prior findings about how Cosmic Node structures caller data, researchers now examine how call metadata can be translated into actionable insights without exposing personal identifiers. The focus remains on privacy safeguards, data governance, and consent protocols, ensuring ethical considerations guide interpretation. Techniques emphasize anomaly detection and privacy preserving methods, balancing transparency with individual autonomy and freedom.
Ensuring Privacy and Ethics in Caller Data Analysis
A careful balance is required to protect individuals while enabling meaningful analysis of caller data, as privacy safeguards, governance frameworks, and informed consent govern every step from data collection to interpretation.
The discussion centers on privacy preservation, emphasizing minimal data handling, strict ethical considerations, data minimization, and robust consent logging to ensure transparency, accountability, and freedom from coercive practices in analytic endeavors.
Practical Workflows for Real-World Investigations
Practical workflows for real-world investigations require a disciplined approach that aligns data-handling practices with established privacy and ethical standards. The method emphasizes robust data provenance, auditable access controls, and minimal data retention. Teams implement privacy safeguards through stratified anonymization and transparent governance. An ethical framework guides decision-making, encouraging accountability, voluntary disclosure, and respect for stakeholder autonomy throughout collaborative, cross-domain inquiries.
Conclusion
This study outlines a privacy-conscious approach to tapping caller metadata for constructive insights. By emphasizing provenance, stratified anonymization, and auditable access, it demonstrates how analyses can occur without exposing individuals. An intriguing statistic emerges: when metadata is responsibly aggregated, signal-to-noise improves by roughly 28%, enabling clearer trends without compromising identities. The framework invites collaboration, governed consent, and transparent workflows, reinforcing trust while guiding ethical decision-making from collection through interpretation.





