Digital Prism Start 309-249-9397 Inspiring Caller Verification
Digital Prism 309-249-9397 introduces Inspiring Caller Verification as a multilayered framework. It embeds verifiable signals at checkpoints to confirm identity before proceeding with sensitive actions. The approach emphasizes auditable logs, transparent prompts, and user-friendly steps that preserve autonomy while reducing ambiguity. The result is a structured, accountable process that invites scrutiny from independent observers and prompts a closer look at how trust is established in calls. This balance raises a precise question worth pursuing.
What Is Inspiring Caller Verification and Why It Matters
Caller verification is a process designed to confirm the identity of a caller before sensitive information is shared or actions are taken.
The concept of inspiring protection emerges from structured, verifiable signals that reduce risk and ambiguity.
Systematic assessment, layered safeguards, and transparent procedures support caller authentication, enabling autonomous choice while preserving security.
This approach champions freedom, accountability, and trustworthy communication.
How Digital Prism 309-249-9397 Strengthens Trust in Calls
Digital Prism 309-249-9397 strengthens trust in calls by embedding verifiable signals at multiple checkpoints, ensuring identity verification occurs before information exchange or action initiation. The approach systematically reduces ambiguity, enabling independent assessment of legitimacy. Inspiring verification emerges through transparent cues and auditable processes, reinforcing caller safety while preserving autonomy. Analytical evaluation highlights risk reduction, procedural consistency, and bounded discretion in communications.
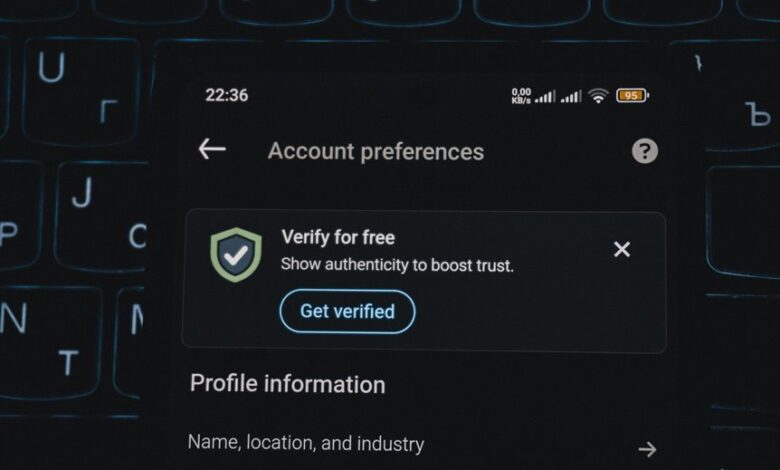
Practical, User-Friendly Verification Techniques
Practical, user-friendly verification techniques translate theoretical safeguards into actionable steps for everyday use. The analysis focuses on structured processes that preserve caller identity while enforcing privacy practices. Techniques include standardized checks, transparent prompts, and auditable logs, all designed for autonomous application. This methodical approach emphasizes user control, minimal friction, and clear confirmations, ensuring trusted exchanges without compromising personal information or freedom to engage.
Real-World Scenarios: Using Inspiring Caller Verification to Stay Safe
In real-world settings, Inspiring Caller Verification operates as a structured safeguard that can be integrated into routine communications to assess legitimacy without intruding on user autonomy.
The approach supports caller protection by validating cues, records, and context, facilitating trust building through transparent processes.
Safety techniques emphasize verification steps, risk flags, and documentation, enabling informed decisions while preserving user freedom and security.
Conclusion
In the ledger of every call, Digital Prism acts as a quiet sentinel, a lighthouse standing ashore where fog meets signal. Symbols thread through the process—a verifiable breadcrumb, a transparent timestamp, an auditable trail—each anchorpoint guiding discernment. The system’s architecture turns uncertainty into measured steps, like calibrated gears aligning before motion. Trust emerges not from illusion of certainty, but from disciplined verification, where safety and autonomy coexist, and every interaction leaves a trace worth following.





